New Delhi, Sep 19: Losing his cool, a senior advocate for Muslim parties in the Ram Janmbhoomi-Babri masjid land dispute case in the Supreme Court, told a curious judge Thursday that he was seeing "some kind of aggression" in his tone.
A five-judge Constitution bench, headed by Chief Justice Ranjan Gogoi, which was hearing the decades-old politically sensitive case on 27th day, did not re-assemble after the lunch break and a source said that the CJI was not feeling well.
"The CJI was a bit unwell that is why the board was discharged post-lunch," the source said.
The bench was earlier questioning senior advocate Rajeev Dhavan, appearing for Sunni Waqf Board and others including original litigant M Siddiq, about the testimony of a witness who had visited the disputed site in 1935 and had deposed before the Allahabad High Court in 2000.
The bench, also comprising justices S A Bobde, D Y Chandrachud, Ashok Bhushan and S A Nazeer, asked Dhavan to read some other portions of the testimony of witness Ram Surat Tiwari dealing with prayers offered by the Hindus at the railings on the disputed site.
"This witness said that he had gone there (site) in 1935... Read his statement, whether we believe it or not is something else," Justice Bhushan asked Dhavan.
"I can see some kind of aggression in My lord's tone," Dhavan said, adding, "If lordships are saying that I am twisting the evidence then I will read that out."
This is not about twisting, the point is whether certain facts are there or not, the judge said.
Senior advocates C S Vaidyanathan and Ranjit Kumar objected to the assertions of Dhavan who quickly apologised to the bench. "My apologies. Sometimes, I am taken aback. I get frightened, what should I do... When there is a hearing which is going on for this long, we sometimes get carried away."
"Dr Dhavan, people who come from the North West Frontier do not get frightened. We are impressed by the history," the CJI observed with a smile.
On Wednesday also, Dhavan had termed as "conjecture" the Supreme Court's observation that the Hindus believed in some divinity in the central dome of the disputed structure at the site which made them offer prayers at the railings put up by the British in 1858. He had quickly apologised.
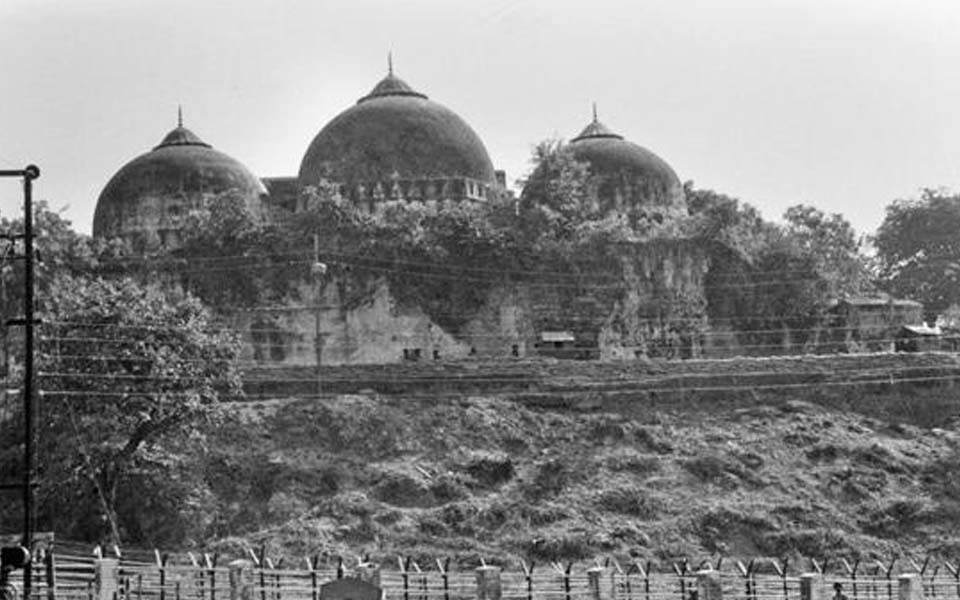
At the outset, Dhavan on Thursday referred to the testimonies of various witnesses, produced by the Hindu side in the High Court, to drive home the point that there was Babri mosque at the site, and they failed to prove the place under the central dome to be the exact birthplace of Lord Ram.
He referred to the suit filed by Nirmohi Akhara's Mahant Raghbar Das in 1885 and said that it was constructing a temple at 'Ram Chabutara' in the outer courtyard of the site.
The Sub Judge, Faizabad, did not allow the petition and there was a finding that Muslims were praying inside and Hindus were offering 'puja' in the outer courtyard, he said.
He again responded to yesterday's observation of the apex court that the 'Ram Chabutara' was set up in the close proximity of the railing because Hindus believed of some divinity in the central dome and this is the reason they were praying at the railing.
There was no evidence that Hindus prayed at the railings or grilled wall, Dhavan said.
He then dealt in detail with the evidence of Tiwari as the top court wanted him to read the testimony in totality to have the clear picture.
He said Tiwari had visited the place with his uncle in December 1935 when he was 12-13 year old said that he had seen one idol and one photograph there at the site.
Dhavan said the witness stated he was an atheist and believed that Lord Ram took birth inside the central dome and described the details in the court in 2000 about what he saw in 1935.
There were many discrepancies in Tiwari's testimony and he is not able to remember anything, he added.
However, the bench said that there was evidence that he had seen the idols inside the central dome before 1949, the year when it was alleged that the idols were placed inside surreptitiously.
All this evidence came after 1989 when the lawsuit on behalf of the deity was filed and these are no credible proofs, Dhavan said, adding that after the 'rath yatra' and demolition of the structure, the Ram Janmbhoomi had become a bigger issue and such testimonies were recorded after these events.
He also referred to principles of law on evidence and said with the "deepest respect" the statements of the witness cannot be regarded as credible proof.
He then reiterated his arguments on 'shebait' (devotee) and next friend and said that idols or deities have to be represented by the 'shebait' only as no other person can have the legal authority to file a lawsuit.
He alleged that Deoki Nandan Agrawal, the next friend of deity 'Ram Lalla', had no locus and the court should not allow such friends as it would affect the legal position on endowment and various land grabbers may emerge to oust 'Shebaits'.
The hearing would continue on Friday.
The Allahabad High Court, in its judgment of 2010 on four civil lawsuits, had partitioned the 2.77-acre disputed land equally among Sunni Waqf Board, Nirmohi Akhara and Ram Lalla. Fourteen appeals have been filed in the Supreme Court against the verdict.
Let the Truth be known. If you read VB and like VB, please be a VB Supporter and Help us deliver the Truth to one and all.
India is witnessing a sharp rise in trojanised Android APK scams, as cybercriminals increasingly exploit fake government, banking, LPG, challan, and welfare scheme apps to seize full remote control of victims’ smartphones.
Cybersecurity investigators warn that attackers are now widely deploying Remote Access Trojan (RAT) malware, often powered by leaked builder kits such as CraxsRAT and heavily modified custom payload frameworks. Once installed, these malicious APKs can convert an ordinary Android phone into a fully controlled fraud device, enabling silent surveillance, banking theft, and mass scam propagation.
These malware campaigns are primarily being distributed through WhatsApp, Telegram, SMS phishing links, and fake APK download websites, where users are tricked into installing apps disguised as:
- e-Challan apps
- SBI KYC verification tools
- PM Yojana portals
- mParivahan clones
- LPG booking apps
- fake adult video call apps
As the scale of the threat intensifies, cybersecurity startup TraceX Labs has introduced TraceX Guard, positioning it as a frontline mobile defence platform against APK fraud, RAT infections, QR scams, and malicious permission abuse.
Fear-Based Social Engineering Behind the Surge
According to investigators, these frauds typically begin with panic-driven social engineering messages sent over WhatsApp or Telegram.
Common bait messages include:
- Your traffic challan has been issued
- Your SBI KYC is pending
- PM Yojana verification required
- Your LPG cylinder booking failed
- Your bank account will be blocked
These alerts often include fake challan numbers, vehicle details, Aadhaar-linked references, or forged bank notices, creating a sense of urgency that pushes victims to install the malicious APK without verification.
One of the most dangerous variants currently in circulation is a fake mParivahan-style application, which closely mimics India’s legitimate transport services interface while secretly embedding a hidden RAT payload.
How the Malware Takes Over Smartphones
Once installed, the malicious APK immediately requests dangerous permissions, including:
- Accessibility access
- SMS permissions
- Call logs
- Notifications
- File storage
- Battery optimization exemptions
Security researchers say Accessibility Service abuse remains the most critical attack vector, allowing the malware to silently:
- read screen contents
- detect banking and UPI apps
- auto-click Allow / Confirm / Pay buttons
- capture OTPs
- launch hidden overlays
- navigate banking sessions
- trigger silent fund transfers
Because these actions occur directly on the victim’s trusted device, attackers are often able to bypass traditional fraud detection systems.
Within minutes, victims may lose control over:
- bank balances
- UPI wallets
- Aadhaar and PAN scans
- contact lists
- personal photos and media
- incoming calls
- SMS OTPs
In many cases, the malware also self-propagates by forwarding malicious APK links through the victim’s own WhatsApp groups and Telegram chats, triggering a chain infection effect across trusted social circles.Fake RTO Challan APKs Become the Most Dangerous Variant
Among the most active campaigns, fake RTO challan APK scams have emerged as one of the most financially destructive.
Victims are first lured into paying a ₹1 “verification fee”, after which the malicious app requests highly sensitive information such as:
- card number
- expiry date
- CVV
- UPI PIN
- net banking credentials
- even ATM PINs
Cybersecurity experts stress that no legitimate government payment system ever asks for an ATM PIN inside an app, making this an immediate red flag.
Once payment details are entered, the embedded RAT intercepts OTPs and silently completes unauthorized transactions.
India’s Mobile Fraud Crisis Reaches Critical Levels
Investigators estimate that more than 70% of reported cyber fraud cases in India now originate from mobile devices, with millions of complaints linked to:
- malicious APKs
- phishing URLs
- QR scams
- RAT droppers
- banking session hijacks
- WhatsApp fraud chains
The impact is particularly severe across Tier-2 and Tier-3 regions, where smartphone adoption has expanded faster than awareness around:
- APK sideloading risks
- dangerous permissions
- fake banking overlays
- accessibility abuse
- WhatsApp APK scams
This has effectively turned Android smartphones into the primary battlefield of India’s financial cybercrime ecosystem.
TraceX Guard Introduced as a Real-Time Defence Layer
In response to this rapidly evolving threat landscape, TraceX Labs has launched TraceX Guard, an AI-powered multilingual Android security suite built specifically for India’s APK fraud ecosystem.
The platform offers:
- real-time APK scanning
- malicious permission detection
- hidden app discovery
- RAT behaviour monitoring
- QR & phishing URL safety grading
- OTP and SIM fraud alerts
- Wi-Fi hotspot verification
- ransomware defence
- India-specific scam intelligence feeds
- support for 10+ regional languages
Its offline-first AI architecture allows users to scan threats without uploading personal data, making it especially useful for privacy-conscious users and low-connectivity regions.
TraceX Labs says the system is specifically trained to detect patterns used in:
- fake challan scams
- counterfeit SBI APKs
- PM Yojana malware
- wedding invitation APK attacks
- honey-trap adult apps
- Telegram-based RAT droppers
From Phishing to Malware-Driven Financial Warfare
Cybersecurity analysts say this marks a major shift in India’s digital threat landscape.
What once began as simple phishing links has now evolved into malware-driven financial warfare at scale, where a single infected smartphone can silently compromise:
- families
- WhatsApp groups
- banking accounts
- local communities
- social trust networks
With losses from mobile-first fraud already running into tens of thousands of crores, experts believe the future of cyber defence will increasingly depend on preventive mobile security tools capable of stopping unsafe APKs before installation.
In that battle, TraceX Guard is emerging as one of the most important first lines of defence for India’s digital users.
Download Now : https://play.google.com/store/apps/details?id=com.tracexlabs.guard