San Francisco (US), Sep 17: The ride-hailing service Uber said on Friday that all its services were operational following what security professionals are calling a major data breach, claiming there was no evidence the hacker got access to sensitive user data.
But the breach, apparently by a lone hacker, put the spotlight on an increasingly effective break-in routine involving social engineering: The hacker apparently gained access posing as a colleague, tricking an Uber employee into surrendering their credentials.
They were then able to locate passwords on the network that got them the level of privileged access reserved for system administrators.
The potential damage was serious: Screenshots the hacker shared with security researchers indicate they obtained full access to the cloud-based systems where Uber stores sensitive customer and financial data.
It is not known how much data the hacker stole or how long they were inside Uber's network. Two researchers who communicated directly with the person who self-identified as an 18-year-old to one of them said they appeared interested in publicity. There was no indication they destroyed data.
But files shared with the researchers and posted widely on Twitter and other social media indicated the hacker was able to access Uber's most crucial internal systems.
"It was really bad the access he had. It's awful," said Corbin Leo, one of the researchers who chatted with the hacker online.
The cybersecurity community's online reaction Uber also suffered a serious 2016 breach was harsh.
The hack "wasn't sophisticated or complicated and clearly hinged on multiple big systemic security culture and engineering failures", tweeted Lesley Carhart, incident response director of Dragos Inc., which specialises in an industrial-control systems.
Leo said screenshots the hacker shared showed the intruder got access to systems stored on Amazon and Google cloud-based servers where Uber keeps source code, financial data and customer data such as driver's licenses.
"If he had keys to the kingdom he could start stopping services. He could delete stuff. He could download customer data, change people's passwords," said Leo, a researcher and head of business development at the security company Zellic.
Screenshots the hacker shared many of which found their way online showed sensitive financial data and internal databases accessed. Also widely circulating online: The hacker announcing the breach Thursday on Uber's internal Slack collaboration system.
Leo, along with Sam Curry, an engineer with Yuga Labs who also communicated with the hacker, said there was no indication that the hacker had done any damage or was interested in anything more than publicity.
"It's pretty clear he's a young hacker because he wants what 99 per cent of what young hackers want, which is fame," Leo said.
Curry said he spoke to several Uber employees on Thursday who said they were "working to lock down everything internally" to restrict the hacker's access. That included the San Francisco company's Slack network, he said.
In a statement posted online on Friday, Uber said "internal software tools that we took down as a precaution yesterday are coming back online".
It said all its services including Uber Eats and Uber Freight were operational and that it had notified law enforcement. The FBI said via email that it is "aware of the cyber incident involving Uber, and our assistance to the company is ongoing".
Uber said there was no evidence that the intruder accessed "sensitive user data" such as trip history but did not respond to questions from The Associated Press including about whether data was stored encrypted.
Curry and Leo said the hacker did not indicate how much data was copied. Uber did not recommend any specific actions for its users, such as changing passwords.
The hacker alerted the researchers to the intrusion on Thursday by using an internal Uber account on the company's network used to post vulnerabilities identified through its bug-bounty programme, which pays ethical hackers to ferret out network weaknesses.
After commenting on those posts, the hacker provided a Telegram account address. Curry and other researchers then engaged them in a separate conversation, where the intruder provided the screenshots as proof.
The AP attempted to contact the hacker at the Telegram account, but received no response.
Screenshots posted online appeared to confirm what the researchers said the hacker claimed: That they obtained privileged access to Uber's most critical systems through social engineering.
The apparent scenario:
The hacker first obtained the password of an Uber employee, likely through phishing. The hacker then bombarded the employee with push notifications asking they confirm a remote log-in to their account.
When the employee did not respond, the hacker reached out via WhatsApp, posing as a fellow worker from the IT department and expressing urgency. Ultimately, the employee caved and confirmed with a mouse click.
Social engineering is a popular hacking strategy, as humans tend to be the weakest link in any network. Teenagers used it in 2020 to hack Twitter and it has more recently been used in hacks of the tech companies Twilio and Cloudflare, said Rachel Tobac, CEO of SocialProof Security, which specialises in training workers not to fall victim to social engineering.
"The hard truth is that most orgs in the world could be hacked in the exact way Uber was just hacked," Tobac tweeted. In an interview, she said "even super tech savvy people fall for social engineering methods every day".
"Attackers are getting better at by-passing or hi-jacking MFA (multi-factor authentication)," said Ryan Sherstobitoff, a senior threat analyst at SecurityScorecard.
That's why many security professionals advocate the use of so-called FIDO physical security keys for user authentication. Adoption of such hardware has been spotty among tech companies, however.
The hack also highlighted the need for real-time monitoring in cloud-based systems to better detect intruders, said Tom Kellermann of Contrast Security.
"Much more attention must be paid to protecting clouds from within" because a single master key can typically unlock all their doors.
Some experts questioned how much cybersecurity has improved at Uber since it was hacked in 2016.
Its former chief security officer, Joseph Sullivan, is currently on trial for allegedly arranging to pay hackers USD 100,000 to cover up that high-tech heist, when the personal information of about 57 million customers and drivers was stolen.
Let the Truth be known. If you read VB and like VB, please be a VB Supporter and Help us deliver the Truth to one and all.
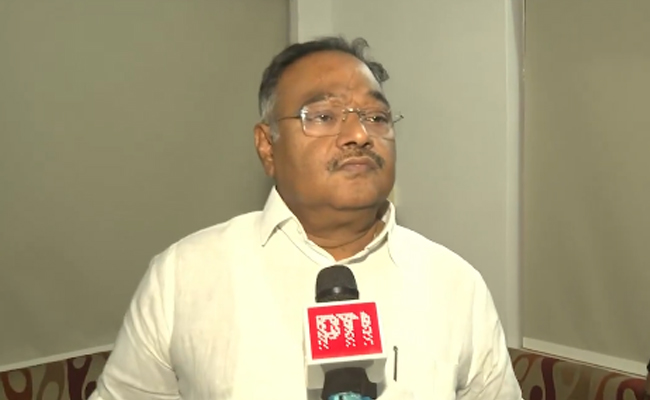
Kolkata (PTI): A day after the BJP's sweeping victory in the West Bengal assembly polls, state party president Samik Bhattacharya on Tuesday urged the administration to act firmly against perpetrators of post-poll violence irrespective of political affiliation.
Addressing reporters after a meeting of the party's top leadership at its Bidhannagar office, Bhattacharya said strict action must be taken against those indulging in violence and warned that BJP workers found involved in such activities would be expelled from the party.
"Post-poll violence would not be tolerated in any form. If anyone from our party is found involved, we will be compelled to remove them," he said.
The BJP leader also appealed to Chief Secretary Dushyant Nariala to ensure prompt administrative intervention wherever incidents of violence are reported.
"I would like to urge the administration to take necessary action wherever such incidents occur. This is precisely why the people of West Bengal have chosen the BJP," he said.
Bhattacharya thanked the electorate for the party's emphatic mandate and expressed gratitude to migrant workers who returned to the state to cast their votes despite logistical challenges.
According to party sources, a high-level meeting was held at the BJP's Bidhannagar office on Tuesday, attended by central observers and senior state leaders, to discuss measures to prevent violence and maintain law and order in the post-result scenario.
The discussions also focused on ensuring that there is no repeat of the violence reported after the 2021 assembly elections, when the BJP had accused the ruling Trinamool Congress of targeting its workers.
The BJP has secured 207 of the 293 seats where polls were held, securing a two-thirds majority and paving the way for its first government in West Bengal. The Trinamool Congress has won 80 seats.
Bhattacharya also appealed to party workers to maintain restraint and not let the victory celebrations turn disruptive.
"I urge our workers to remain peaceful, stay happy, and fulfil the responsibilities given by the party. Do not hurt anyone in the name of celebration, and do not hurt anyone's sentiments," he said.